Users of Chromium-based web browsers, including Google Chrome, Microsoft Edge, Vivaldi, and Brave, are urged to update their software immediately following the discovery and rapid patching of a high-severity zero-day vulnerability, identified as CVE-2026-2441. This critical flaw, described as a "Use-After-Free in CSS," allowed remote attackers to execute arbitrary code within the browser’s sandbox environment through specially crafted HTML pages. The vulnerability’s discovery and subsequent exploitation "in the wild" prompted an urgent response from Google and other browser developers, culminating in a patch released on Friday, February 13, 2026.
Understanding the Immediate Threat and Required Actions
The "Use-After-Free" (UAF) vulnerability, while technically residing within the browser’s CSS rendering engine, posed a significant risk. If exploited, it could grant an attacker control over a user’s browser, potentially leading to data theft, system compromise, or further malicious activities. The swift action by browser vendors underscores the severity of the threat and the urgency for users to update.
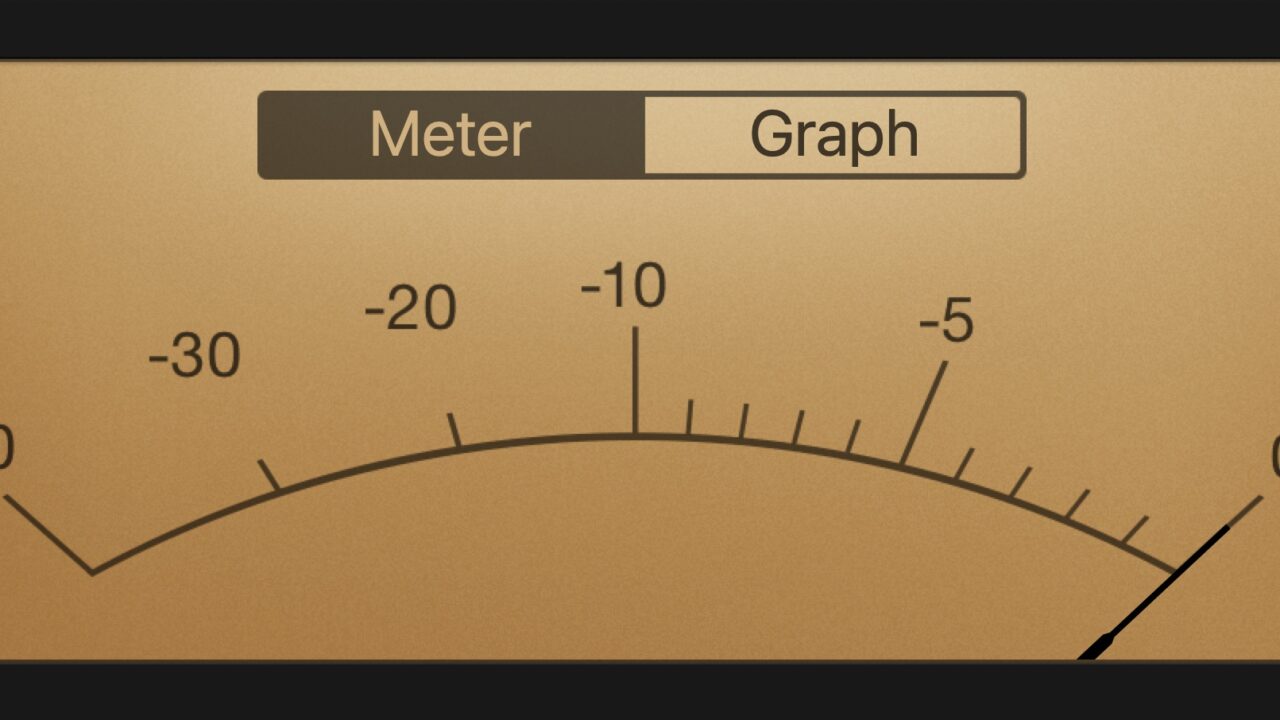
To ascertain safety and apply the necessary patch, users should verify their browser versions against the following table and update promptly:
| Chromium-based Browser | Minimum Safe Version | Update Instructions |
|---|---|---|
| Google Chrome | 145.7632.75 or later | Go to Settings > About Chrome and check for updates. The browser will typically download and install the update automatically upon relaunch. |
| Microsoft Edge | 145.0.3800.58 or later | Click on the three dots (…) on the very right-hand side of the window, then select Help and Feedback > About Microsoft Edge. |
| Vivaldi | 7.8 or later | Click the V icon (menu) in the top-left corner, select Help > About. |
| Brave | v1.87.188 or later | Click the hamburger menu on the top right, select Help > About Brave. |
These updates are designed to close the exploit vector and protect users from ongoing threats. Failure to update leaves systems vulnerable to known and actively exploited attacks.
Chronology of a Critical Discovery and Rapid Response
The timeline surrounding CVE-2026-2441 highlights the vigilance of the cybersecurity community and the rapid response mechanisms in place for critical browser vulnerabilities:
- Early February 2026: Security researcher Shaheen Fazim identifies and responsibly reports a critical Use-After-Free vulnerability within Google Chrome’s Blink rendering engine. Fazim, known as a professional bug hunter with a track record of discovering significant flaws, submitted the details to Google’s Vulnerability Rewards Program.
- February 13, 2026: Google publicly acknowledges the vulnerability and releases an emergency stable channel update for desktop browsers. The Chrome Releases blog announces the patch for a "high-severity" vulnerability, specifically noting "User after free in CSS." Crucially, Google’s statement includes the alarming disclosure: "Google is aware that an exploit for CVE-2026-2441 exists in the wild." This indicates that malicious actors were already leveraging the flaw before the patch was widely available.
- Following Days: Other Chromium-based browser developers, including Microsoft (Edge), Vivaldi, and Brave, rapidly integrate Google’s patch into their respective browser versions and release updates to their user bases, typically within hours or a few days of Google’s initial release. This synchronized response is standard practice within the Chromium ecosystem to ensure broad user protection.
- NIST NVD Listing: The National Vulnerability Database (NVD) formally lists the vulnerability as CVE-2026-2441, providing a detailed description: "In CSS in Google Chrome before 145.0.7632.75 allowed a remote attacker to execute arbitrary code inside a sandbox via a crafted HTML page." This official listing by a government agency underscores the severity and widespread impact of the flaw.
The rapid turnaround from discovery to public patch, particularly with an "in the wild" exploitation warning, demonstrates the urgency with which browser vendors address such critical security issues.
Deconstructing the "CSS Exploit" Misconception
Initially, headlines and initial reports surrounding CVE-2026-2441 caused confusion, leading many to believe that the vulnerability was a "pure CSS exploit." This interpretation suggested that malicious CSS alone could compromise a system, a notion that challenged long-held assumptions about the inherent security of CSS. However, a deeper technical analysis clarifies the true nature of the vulnerability.
While the vulnerability is indeed categorized as "User after free in CSS," implying a CSS-related component, the malicious action is not performed by CSS directly. Instead, the CSS code creates a specific memory state within the browser’s rendering engine that a malicious JavaScript payload then exploits.
The core of the issue lies in Google Chrome’s Blink CSS engine component. Specifically, the vulnerability exploited a flaw in how Chrome managed the memory for CSSFontFeaturesValueMap objects, which are generated when parsing the @font-feature-values CSS rule. This rule, used for defining custom font features, has been available since early 2023.
Consider the following CSS snippet that, while benign in itself, could trigger the vulnerable memory condition:
@font-feature-values VulnTestFont
@styleset
entry_a: 1;
entry_b: 2;
entry_c: 3;
entry_d: 4;
entry_e: 5;
entry_f: 6;
entry_g: 7;
entry_h: 8;
When Chrome’s Blink engine parses this CSS, a CSSFontFeaturesValueMap object is created and added to the document.styleSheets[0].cssRules collection. The underlying data structure for this map, a HashMap, was subject to a memory management bug. This bug inadvertently allowed a malicious script to access memory that had already been freed and potentially reallocated for another purpose.
This scenario is the hallmark of a "Use-After-Free" (UAF) vulnerability. In UAF attacks, a program attempts to use a memory location after it has been freed. If an attacker can control the contents of that freed memory before it is reused, they can inject malicious data or code. This can lead to various outcomes, from browser crashes to, in severe cases like CVE-2026-2441, arbitrary code execution. The JavaScript component of the exploit would be responsible for manipulating memory allocation and deallocation to trigger the UAF condition and then executing malicious code within the re-controlled memory region. This is a critical distinction from a purely CSS-driven attack, which would typically involve data exfiltration or UI manipulation rather than direct code execution.
The Perils of Use-After-Free Vulnerabilities
Use-After-Free vulnerabilities are a notorious class of memory safety issues, particularly prevalent in programming languages like C and C++ that require manual memory management. They arise when a pointer references a memory location that has been deallocated, but the program later attempts to use that pointer. This creates a window of opportunity for an attacker.
The severity of UAF bugs stems from their potential to lead to arbitrary code execution. Once an attacker can reliably trigger a UAF condition, they can often craft a sequence of operations:
- Free a specific block of memory.
- Allocate a new block of memory, ensuring it occupies the same physical memory address as the previously freed block.
- Fill this new block with attacker-controlled data, often a malicious payload or pointers to such payloads.
- Trigger the "use" of the old, freed pointer, which now inadvertently points to the attacker’s data.
This process can lead to "type confusion," where the program expects one type of data at a memory address but finds another, allowing the attacker to subvert program logic. In the context of CVE-2026-2441, the UAF in the CSSFontFeaturesValueMap allowed JavaScript to interact with memory in an unintended way, ultimately leading to the ability to execute arbitrary code.
Modern operating systems employ various exploit mitigation techniques, such as Address Space Layout Randomization (ASLR) and Data Execution Prevention (DEP), which make UAF exploitation significantly more challenging. Attackers must often chain multiple vulnerabilities or employ complex memory spray techniques to bypass these protections and achieve reliable code execution. The fact that an exploit for CVE-2026-2441 existed "in the wild" suggests that sophisticated adversaries successfully navigated these defenses.
The Role of Bug Bounty Programs and Security Researchers
The discovery of CVE-2026-2441 by Shaheen Fazim highlights the invaluable role of independent security researchers and bug bounty programs in bolstering software security. Fazim, described as a professional bug hunter, likely received a substantial reward from Google for reporting such a critical zero-day vulnerability that was actively being exploited. Google’s bug bounty program is one of the most generous in the industry, offering significant payouts for high-impact vulnerabilities, especially those with "in the wild" exploitation. These programs incentivize ethical hackers to find and responsibly disclose flaws before they can be widely abused, acting as a crucial line of defense in the ever-evolving cybersecurity landscape. Without such efforts, many critical vulnerabilities might remain undiscovered until exploited by malicious actors, leading to widespread compromise.
Broader Implications: The Shift Towards Memory-Safe Languages
The recurring nature of Use-After-Free vulnerabilities in Chromium-based browsers, and indeed across many large C/C++ codebases, has spurred a significant industry-wide discussion about the adoption of memory-safe programming languages. Google’s own security reports consistently show that a substantial percentage of critical vulnerabilities in Chrome are memory safety bugs.
Mozilla Firefox, for instance, took a proactive step years ago by rewriting significant portions of its CSS renderer, Quantum CSS (also known as Stylo), in Rust. Rust is a modern systems programming language designed with memory safety as a core principle. Its ownership and borrowing system, enforced at compile time, prevents common memory errors like UAF, null pointer dereferences, and data races without relying on a garbage collector or runtime overhead. This approach significantly reduces the attack surface for an entire class of vulnerabilities.
Recognizing the benefits, Google officially announced its support for the use of Rust in Chromium in 2023. The motivations articulated by Google were clear: "safer (less complex C++ overall, no memory safety bugs in a sandbox either)" and to "improve the security (increasing the number of lines of code without memory safety bugs, decreasing the bug density of code) of Chrome." While the full transition of critical components from C++ to Rust will be a gradual and monumental effort, the incident with CVE-2026-2441 serves as a stark reminder of the ongoing need for such a holistic approach to memory safety.
The continuous battle against memory safety bugs in widely used software like web browsers underscores the complexity of modern software development. As long as significant portions of critical infrastructure remain written in languages prone to these types of errors, vulnerabilities like CVE-2026-2441 will continue to emerge. The long-term trend suggests an accelerating shift towards memory-safe languages to fundamentally reduce the occurrence of these high-severity flaws, ultimately enhancing the security posture of the digital world. For now, prompt user updates remain the most critical immediate defense.