The landscape of business-to-business (B2B) client acquisition has undergone a fundamental transformation as solo founders and independent consultants seek scalable ways to secure high-ticket contracts. In an era where manual networking and traditional advertising are increasingly fragmented, structured email outreach has emerged as a primary driver of growth for small-scale enterprises. However, the efficacy of this channel is currently dictated by rigorous technical standards and evolving algorithm-based filters implemented by major service providers. For the modern entrepreneur, the transition from sporadic "cold emailing" to a professional outreach engine is no longer a luxury but a requirement for operational survival.
The Evolution of Digital Prospecting and the 2024 Compliance Shift
The shift toward more disciplined outreach began in earnest during the early 2020s, but it reached a critical juncture in February 2024. During this period, major email service providers (ESPs), specifically Google and Yahoo, implemented stringent new requirements for bulk senders. These updates mandated the use of advanced authentication protocols and established a strict spam rate threshold of 0.3%. For solo founders, these changes effectively ended the era of "batch and blast" messaging.
Industry data indicates that email remains the highest-ROI marketing channel, with the Data & Marketing Association reporting an average return of $36 for every $1 invested. Despite this potential, approximately 20% of commercial emails fail to reach the primary inbox, according to deliverability benchmarks from Return Path. This discrepancy highlights a growing divide between founders who master the technical nuances of the medium and those who risk their digital reputation through outdated practices.
Establishing the Technical Infrastructure: The Dedicated Domain Strategy
The primary risk identified by cybersecurity experts and deliverability consultants is the contamination of a primary business domain. When a solo founder uses their main operational email—the one used for client invoices and project management—for cold outreach, they expose their entire business infrastructure to "domain blacklisting." If a high volume of recipients marks these outreach emails as spam, the domain’s reputation drops, potentially causing legitimate, high-priority client communications to be diverted to junk folders.
To mitigate this, a professional outreach system requires the registration of a "look-alike" or "shadow" domain. For example, if a consultant operates under "consultancy.com," their outreach efforts might originate from "getconsultancy.com" or "consultancy.io." This isolation ensures that even if an outreach campaign faces deliverability challenges, the primary business operations remain unaffected.

The Three Pillars of Email Authentication: SPF, DKIM, and DMARC
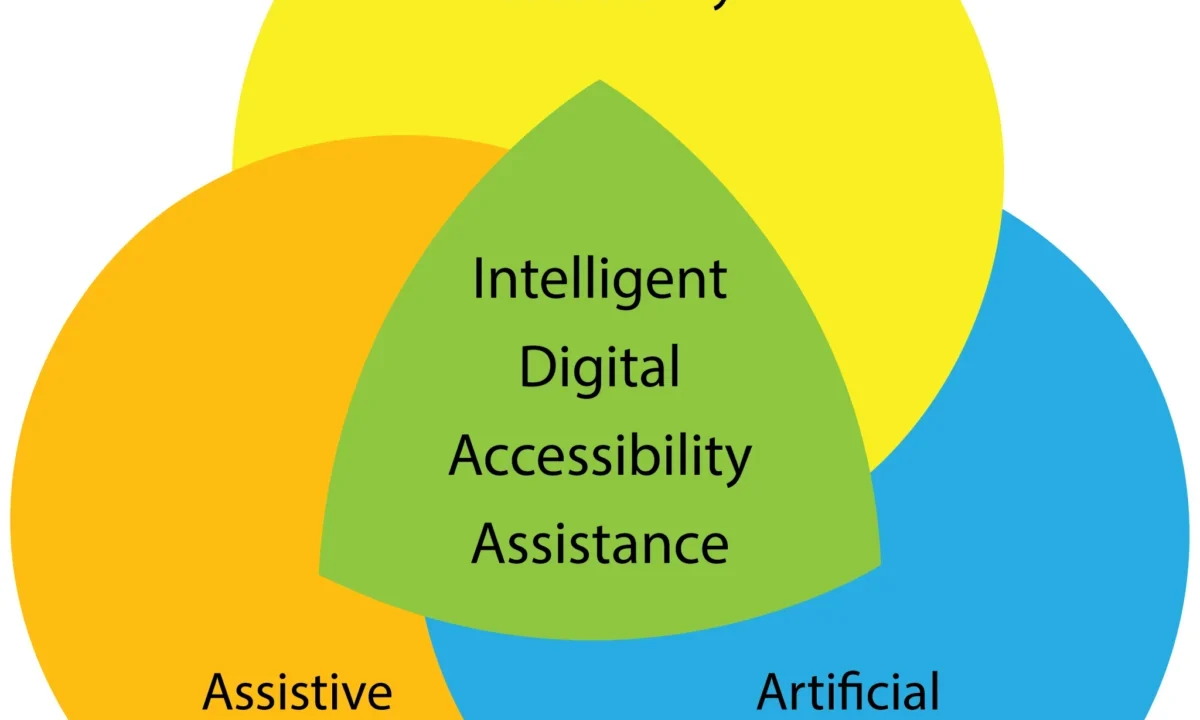
The contemporary news cycle surrounding digital security frequently cites the rise of phishing and spoofing. In response, ESPs rely on three specific DNS (Domain Name System) records to verify a sender’s identity.
- Sender Policy Framework (SPF): This record provides a list of authorized IP addresses and domains allowed to send emails on behalf of the domain. It acts as a digital whitelist for receiving servers.
- DomainKeys Identified Mail (DKIM): This protocol adds a cryptographic signature to every email sent. It ensures that the content of the message has not been tampered with during transit.
- Domain-based Message Authentication, Reporting, and Conformance (DMARC): This is a policy layer that tells receiving servers what to do if an email fails SPF or DKIM checks. A "p=quarantine" or "p=reject" policy is increasingly becoming the industry standard for high-reputation senders.
Failure to implement these three records is cited by deliverability analysts as the leading cause of immediate "spam folder" placement for new domains.
The Chronology of the Inbox Warm-Up Process
A common error among solo founders is the immediate launch of high-volume campaigns on newly registered domains. This behavior mirrors the patterns of malicious actors, triggering "new domain" filters at the ISP level. A sustainable outreach system follows a specific chronological warm-up sequence:
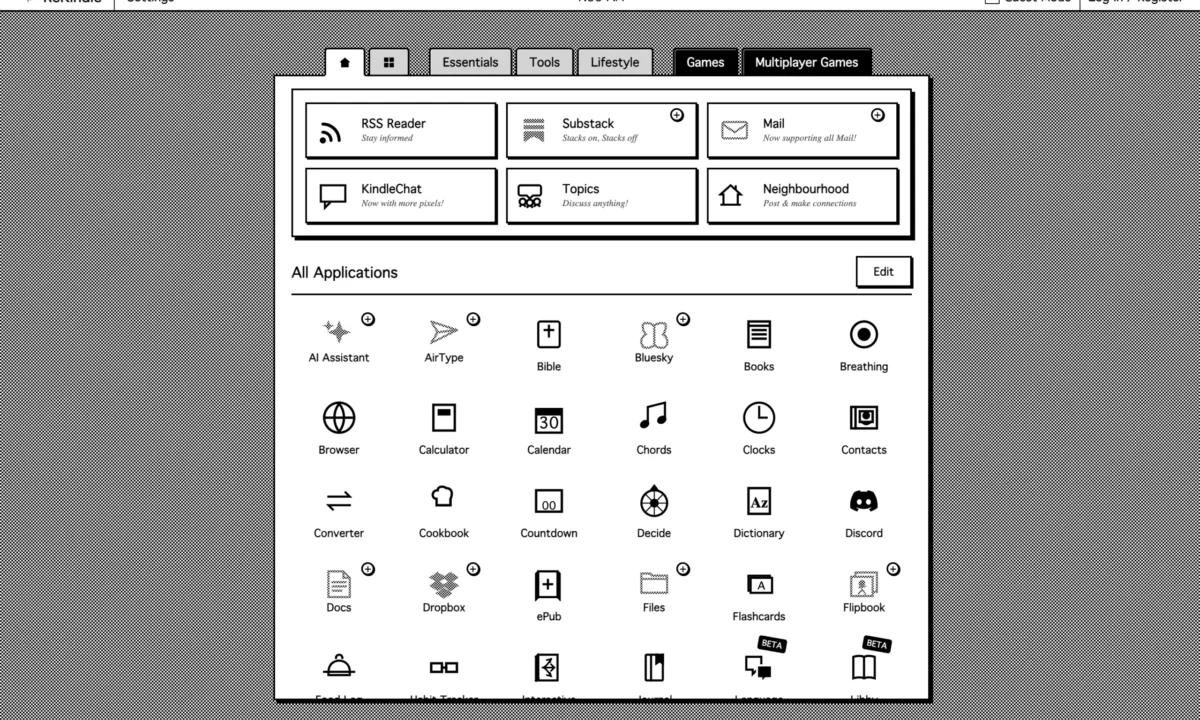
- Weeks 1-2: Internal Seeding. The domain is used to send a low volume of emails to known contacts or internal addresses. This period focuses on establishing a baseline of "opens" and "replies," which are the strongest positive signals for ISP algorithms.
- Weeks 3-4: Automated Warm-Up. Founders often utilize specialized "inbox warm-up" tools. These platforms create a peer-to-peer network where automated accounts exchange emails, move them out of the spam folder, and mark them as important. This simulates organic human behavior.
- Month 2 and Beyond: Incremental Scaling. Only after a domain has achieved a high "Sender Score" does the founder begin to increase daily volume. Experts recommend starting with 5–10 emails per day and gradually increasing by 10-20% weekly until reaching a sustainable limit, typically capped at 50 messages per day per inbox to avoid detection by anti-spam heuristics.
Content Optimization: Personalization vs. Algorithmic Triggers
The content of the outreach email itself is a critical factor in deliverability. Modern spam filters employ natural language processing (NLP) to detect promotional patterns. Journalistic analysis of successful outreach campaigns suggests that brevity and personalization are the two most significant predictors of success.
Generic templates, often found in "growth hacking" communities, are frequently flagged because they share "fingerprints" with thousands of other spam messages. To counter this, solo founders must prioritize "hyper-personalization." This involves referencing specific recent achievements, public statements, or unique pain points of the prospect.
Furthermore, the avoidance of "spam trigger words" remains essential. Phrases such as "free," "guaranteed," "buy now," or "risk-free" can increase the spam score of a message. Technical testing of emails prior to launch—using tools that simulate placement across Gmail, Outlook, and iCloud—allows founders to catch these triggers before they impact a live campaign.
List Hygiene and Data Integrity
The health of a prospect list is a direct reflection of a founder’s research quality. The purchase of bulk email lists is widely condemned by industry veterans as a "reputation killer." Purchased lists often contain "spam traps"—email addresses that no longer belong to humans but are monitored by ISPs to identify and blacklist bulk senders.
Effective outreach requires a commitment to "list hygiene." This includes:
- Verification: Using API-based verification services to ensure every email address is active before sending.
- Bounce Monitoring: Immediately removing addresses that result in a "hard bounce" (permanent delivery failure). A bounce rate exceeding 2% is generally considered a red flag for ESPs.
- Relevance Mapping: Ensuring the prospect’s current role and company size align with the consultant’s service offering, thereby reducing the likelihood of a manual "Report Spam" click.
Broader Impact and Industry Implications
The professionalization of solo founder outreach has broader implications for the freelance and consulting economy. As the barrier to entry for effective outreach rises, those who invest in technical infrastructure gain a significant competitive advantage. This trend is likely to lead to a "quality over quantity" shift in the market.
Analysts suggest that the integration of Artificial Intelligence (AI) will further complicate this landscape. While AI can assist in personalization, it can also be used by ISPs to detect and block AI-generated outreach at scale. The future of the industry lies in a "hybrid" approach, where automated systems handle the technical deliverability and data management, while human founders provide the strategic insight and genuine relationship-building that algorithms cannot replicate.
Conclusion: Outreach as Business Infrastructure
Treating email outreach as a one-time marketing tactic is a strategy that leads to diminishing returns and technical debt. Instead, solo founders must view their outreach engine as a vital piece of business infrastructure, akin to a legal entity or a financial accounting system.
By establishing dedicated domains, securing authentication protocols, and adhering to a disciplined warm-up and hygiene schedule, founders protect their most valuable asset: their reputation. In a digital economy where visibility is synonymous with opportunity, the ability to reliably land in a prospect’s inbox is the ultimate competitive edge. As the technical requirements for email continue to evolve, the founders who prioritize deliverability will be the ones who secure the most sustainable and high-value client relationships.